- The previous commit (
|
||
|---|---|---|
| .github/workflows | ||
| clusters | ||
| doc/images | ||
| galaxies | ||
| misp | ||
| tools | ||
| vocabularies | ||
| .gitchangelog.rc | ||
| .gitignore | ||
| .travis.yml | ||
| CONTRIBUTE.md | ||
| jq_all_the_things.sh | ||
| LICENSE.md | ||
| README.md | ||
| schema_clusters.json | ||
| schema_galaxies.json | ||
| schema_misp.json | ||
| schema_vocabularies.json | ||
| validate_all.sh | ||
misp-galaxy
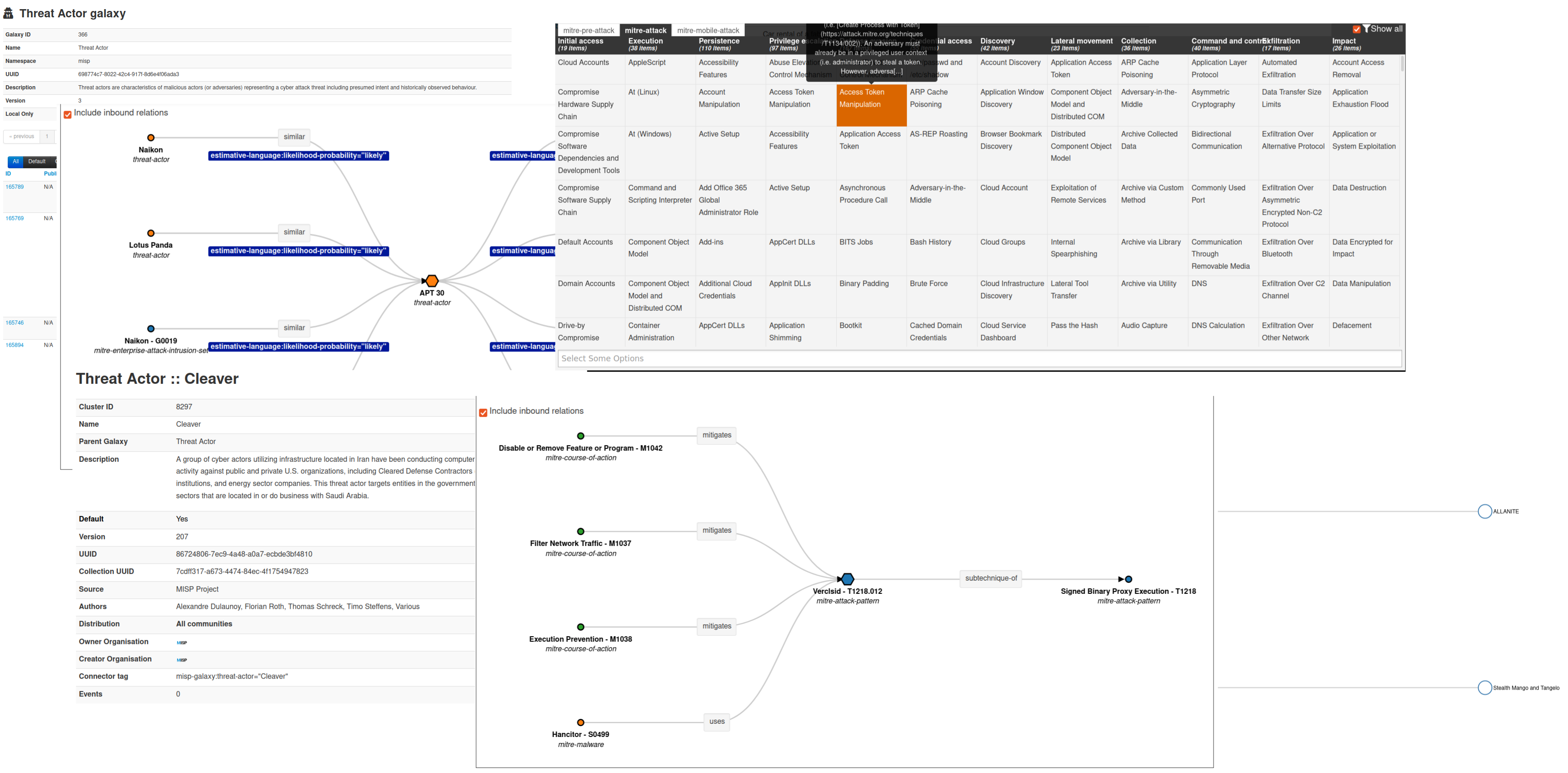
MISP galaxy is a simple method to express a large object called cluster that can be attached to MISP events or attributes. A cluster can be composed of one or more elements. Elements are expressed as key-values. There are default knowledge base (such as Threat Actors, Tools, Ransomware, ATT&CK matrixes) available in MISP galaxy but those can be overwritten, replaced, updated, forked and shared as you wish.
Existing clusters and vocabularies can be used as-is or as a common knowledge base. MISP distribution can be applied to each cluster to permit a limited or broader distribution scheme.
Galaxies can be also used to expressed existing matrix-like standards such as MITRE ATT&CK(tm) or custom ones.
The objective is to have a comment set of clusters for organizations starting analysis but that can be expanded to localized information (which is not shared) or additional information (that can be shared).
Available Galaxy - clusters
360.net Threat Actors
360.net Threat Actors - Known or estimated adversary groups as identified by 360.net.
Category: actor - source: https://apt.360.net/aptlist - total: 42 elements
Android
Android - Android malware galaxy based on multiple open sources.
Category: tool - source: Open Sources - total: 431 elements
Azure Threat Research Matrix
Azure Threat Research Matrix - The purpose of the Azure Threat Research Matrix (ATRM) is to educate readers on the potential of Azure-based tactics, techniques, and procedures (TTPs). It is not to teach how to weaponize or specifically abuse them. For this reason, some specific commands will be obfuscated or parts will be omitted to prevent abuse.
Category: atrm - source: https://github.com/microsoft/Azure-Threat-Research-Matrix - total: 89 elements
attck4fraud
attck4fraud - attck4fraud - Principles of MITRE ATT&CK in the fraud domain
Category: guidelines - source: Open Sources - total: 31 elements
Backdoor
Backdoor - A list of backdoor malware.
Category: tool - source: Open Sources - total: 12 elements
Banker
Banker - A list of banker malware.
Category: tool - source: Open Sources - total: 52 elements
Bhadra Framework
Bhadra Framework - Bhadra Threat Modeling Framework
Category: mobile - source: https://arxiv.org/pdf/2005.05110.pdf - total: 47 elements
Botnet
Botnet - botnet galaxy
Category: tool - source: MISP Project - total: 73 elements
Branded Vulnerability
Branded Vulnerability - List of known vulnerabilities and attacks with a branding
Category: vulnerability - source: Open Sources - total: 14 elements
Cert EU GovSector
Cert EU GovSector - Cert EU GovSector
Category: sector - source: CERT-EU - total: 6 elements
China Defence Universities Tracker
China Defence Universities Tracker - The China Defence Universities Tracker is a database of Chinese institutions engaged in military or security-related science and technology research. It was created by ASPI’s International Cyber Policy Centre.
Category: academic-institution - source: ASPI International Cyber Policy Centre - total: 159 elements
CONCORDIA Mobile Modelling Framework - Attack Pattern
CONCORDIA Mobile Modelling Framework - Attack Pattern - A list of Techniques in CONCORDIA Mobile Modelling Framework.
Category: cmtmf-attack-pattern - source: https://5g4iot.vlab.cs.hioa.no/ - total: 93 elements
Country
Country - Country meta information based on the database provided by geonames.org.
Category: country - source: MISP Project - total: 252 elements
Cryptominers
Cryptominers - A list of cryptominer and cryptojacker malware.
Category: Cryptominers - source: Open Source Intelligence - total: 4 elements
Election guidelines
Election guidelines - Universal Development and Security Guidelines as Applicable to Election Technology.
Category: guidelines - source: Open Sources - total: 23 elements
Exploit-Kit
Exploit-Kit - Exploit-Kit is an enumeration of some exploitation kits used by adversaries. The list includes document, browser and router exploit kits.It's not meant to be totally exhaustive but aim at covering the most seen in the past 5 years
Category: tool - source: MISP Project - total: 52 elements
Malpedia
Malpedia - Malware galaxy cluster based on Malpedia.
Category: tool - source: Malpedia - total: 2462 elements
Microsoft Activity Group actor
Microsoft Activity Group actor - Activity groups as described by Microsoft
Category: actor - source: MISP Project - total: 14 elements
Misinformation Pattern
Misinformation Pattern - AM!TT Technique
Category: misinformation-pattern - source: https://github.com/misinfosecproject/amitt_framework - total: 61 elements
Attack Pattern
Attack Pattern - ATT&CK tactic
Category: attack-pattern - source: https://github.com/mitre/cti - total: 1003 elements
Course of Action
Course of Action - ATT&CK Mitigation
Category: course-of-action - source: https://github.com/mitre/cti - total: 279 elements
Enterprise Attack - Attack Pattern
Enterprise Attack - Attack Pattern - ATT&CK tactic
Category: attack-pattern - source: https://github.com/mitre/cti - total: 219 elements
Enterprise Attack - Course of Action
Enterprise Attack - Course of Action - ATT&CK Mitigation
Category: course-of-action - source: https://github.com/mitre/cti - total: 215 elements
Enterprise Attack - Intrusion Set
Enterprise Attack - Intrusion Set - Name of ATT&CK Group
Category: actor - source: https://github.com/mitre/cti - total: 69 elements
Enterprise Attack - Malware
Enterprise Attack - Malware - Name of ATT&CK software
Category: tool - source: https://github.com/mitre/cti - total: 188 elements
Enterprise Attack - Tool
Enterprise Attack - Tool - Name of ATT&CK software
Category: tool - source: https://github.com/mitre/cti - total: 45 elements
Assets
Assets - A list of asset categories that are commonly found in industrial control systems.
Category: asset - source: https://collaborate.mitre.org/attackics/index.php/All_Assets - total: 7 elements
Groups
Groups - Groups are sets of related intrusion activity that are tracked by a common name in the security community. Groups are also sometimes referred to as campaigns or intrusion sets. Some groups have multiple names associated with the same set of activities due to various organizations tracking the same set of activities by different names. Groups are mapped to publicly reported technique use and referenced in the ATT&CK for ICS knowledge base. Groups are also mapped to reported software used during intrusions.
Category: actor - source: https://collaborate.mitre.org/attackics/index.php/Groups - total: 10 elements
Levels
Levels - Based on the Purdue Model to aid ATT&CK for ICS users to understand which techniques are applicable to their environment.
Category: level - source: https://collaborate.mitre.org/attackics/index.php/All_Levels - total: 3 elements
Software
Software - Software is a generic term for custom or commercial code, operating system utilities, open-source software, or other tools used to conduct behavior modeled in ATT&CK for ICS.
Category: tool - source: https://collaborate.mitre.org/attackics/index.php/Software - total: 17 elements
Tactics
Tactics - A list of all 11 tactics in ATT&CK for ICS
Category: tactic - source: https://collaborate.mitre.org/attackics/index.php/All_Tactics - total: 9 elements
Techniques
Techniques - A list of Techniques in ATT&CK for ICS.
Category: attack-pattern - source: https://collaborate.mitre.org/attackics/index.php/All_Techniques - total: 78 elements
Intrusion Set
Intrusion Set - Name of ATT&CK Group
Category: actor - source: https://github.com/mitre/cti - total: 138 elements
Malware
Malware - Name of ATT&CK software
Category: tool - source: https://github.com/mitre/cti - total: 598 elements
Mobile Attack - Attack Pattern
Mobile Attack - Attack Pattern - ATT&CK tactic
Category: attack-pattern - source: https://github.com/mitre/cti - total: 76 elements
Mobile Attack - Course of Action
Mobile Attack - Course of Action - ATT&CK Mitigation
Category: course-of-action - source: https://github.com/mitre/cti - total: 14 elements
Mobile Attack - Intrusion Set
Mobile Attack - Intrusion Set - Name of ATT&CK Group
Category: actor - source: https://github.com/mitre/cti - total: 1 elements
Mobile Attack - Malware
Mobile Attack - Malware - Name of ATT&CK software
Category: tool - source: https://github.com/mitre/cti - total: 35 elements
Mobile Attack - Tool
Mobile Attack - Tool - Name of ATT&CK software
Category: tool - source: https://github.com/mitre/cti - total: 1 elements
Pre Attack - Attack Pattern
Pre Attack - Attack Pattern - ATT&CK tactic
Category: attack-pattern - source: https://github.com/mitre/cti - total: 174 elements
Pre Attack - Intrusion Set
Pre Attack - Intrusion Set - Name of ATT&CK Group
Category: actor - source: https://github.com/mitre/cti - total: 7 elements
Tool
Tool - Name of ATT&CK software
Category: tool - source: https://github.com/mitre/cti - total: 80 elements
o365-exchange-techniques
o365-exchange-techniques - o365-exchange-techniques - Office365/Exchange related techniques by @johnLaTwC and @inversecos
Category: guidelines - source: Open Sources, https://www.inversecos.com/2021/09/office365-attacks-bypassing-mfa.html - total: 62 elements
Preventive Measure
Preventive Measure - Preventive measures based on the ransomware document overview as published in https://docs.google.com/spreadsheets/d/1TWS238xacAto-fLKh1n5uTsdijWdCEsGIM0Y0Hvmc5g/pubhtml# . The preventive measures are quite generic and can fit any standard Windows infrastructure and their security measures.
Category: measure - source: MISP Project - total: 20 elements
Ransomware
Ransomware - Ransomware galaxy based on https://docs.google.com/spreadsheets/d/1TWS238xacAto-fLKh1n5uTsdijWdCEsGIM0Y0Hvmc5g/pubhtml and http://pastebin.com/raw/GHgpWjar
Category: tool - source: Various - total: 1610 elements
RAT
RAT - remote administration tool or remote access tool (RAT), also called sometimes remote access trojan, is a piece of software or programming that allows a remote "operator" to control a system as if they have physical access to that system.
Category: tool - source: MISP Project - total: 264 elements
Regions UN M49
Regions UN M49 - Regions based on UN M49.
Category: location - source: https://unstats.un.org/unsd/methodology/m49/overview/ - total: 31 elements
rsit
rsit - rsit
Category: rsit - source: https://github.com/enisaeu/Reference-Security-Incident-Taxonomy-Task-Force - total: 39 elements
Sector
Sector - Activity sectors
Category: sector - source: CERT-EU - total: 117 elements
Dark Patterns
Dark Patterns - Dark Patterns are user interface that tricks users into making decisions that benefit the interface's holder to the expense of the user.
Category: dark-patterns - source: CIRCL - total: 19 elements
SoD Matrix
SoD Matrix - SOD Matrix
Category: sod-matrix - source: https://github.com/cudeso/SoD-Matrix - total: 276 elements
Stealer
Stealer - A list of malware stealer.
Category: tool - source: Open Sources - total: 6 elements
Surveillance Vendor
Surveillance Vendor - List of vendors selling surveillance technologies including malware, interception devices or computer exploitation services.
Category: actor - source: MISP Project - total: 15 elements
Target Information
Target Information - Description of targets of threat actors.
Category: target - source: Various - total: 240 elements
TDS
TDS - TDS is a list of Traffic Direction System used by adversaries
Category: tool - source: MISP Project - total: 10 elements
Tea Matrix
Tea Matrix - Tea Matrix
Category: tea-matrix - source: ** - total: 7 elements
Threat Actor
Threat Actor - Known or estimated adversary groups targeting organizations and employees. Adversary groups are regularly confused with their initial operation or campaign. threat-actor-classification meta can be used to clarify the understanding of the threat-actor if also considered as operation, campaign or activity group.
Category: actor - source: MISP Project - total: 397 elements
Tool
Tool - threat-actor-tools is an enumeration of tools used by adversaries. The list includes malware but also common software regularly used by the adversaries.
Category: tool - source: MISP Project - total: 537 elements
Online documentation
A readable PDF overview of the MISP galaxy is available or HTML and generated from the JSON.
How to contribute?
License
The MISP galaxy (JSON files) are dual-licensed under:
- CC0 1.0 Universal (CC0 1.0) - Public Domain Dedication.
or
Copyright (c) 2015-2022 Alexandre Dulaunoy - a@foo.be
Copyright (c) 2015-2022 CIRCL - Computer Incident Response Center Luxembourg
Copyright (c) 2015-2022 Andras Iklody
Copyright (c) 2015-2022 Raphael Vinot
Copyright (c) 2015-2022 Deborah Servili
Copyright (c) 2016-2022 Various contributors to MISP Project
Redistribution and use in source and binary forms, with or without modification,
are permitted provided that the following conditions are met:
1. Redistributions of source code must retain the above copyright notice,
this list of conditions and the following disclaimer.
2. Redistributions in binary form must reproduce the above copyright notice,
this list of conditions and the following disclaimer in the documentation
and/or other materials provided with the distribution.
THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS "AS IS" AND
ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED
WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED.
IN NO EVENT SHALL THE COPYRIGHT HOLDER OR CONTRIBUTORS BE LIABLE FOR ANY DIRECT,
INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING,
BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE,
DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF
LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE
OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED
OF THE POSSIBILITY OF SUCH DAMAGE.