mirror of
https://github.com/MISP/misp-galaxy.git
synced 2024-11-26 16:57:18 +00:00
merge
This commit is contained in:
commit
e523bdaf70
12 changed files with 1676 additions and 67 deletions
|
|
@ -13,7 +13,7 @@ jobs:
|
||||||
runs-on: ubuntu-latest
|
runs-on: ubuntu-latest
|
||||||
strategy:
|
strategy:
|
||||||
matrix:
|
matrix:
|
||||||
python-version: [3.6, 3.7, 3.8, 3.9]
|
python-version: [3.8, 3.9, '3.10']
|
||||||
|
|
||||||
steps:
|
steps:
|
||||||
|
|
||||||
|
|
@ -48,5 +48,5 @@ jobs:
|
||||||
- name: Test with Python module
|
- name: Test with Python module
|
||||||
run: |
|
run: |
|
||||||
pushd PyMISPGalaxies
|
pushd PyMISPGalaxies
|
||||||
poetry run nosetests-3.4 --with-coverage --cover-package=pymispgalaxies -d
|
poetry run pytest --cov=pymispgalaxies tests/tests.py
|
||||||
popd
|
popd
|
||||||
1
.gitignore
vendored
1
.gitignore
vendored
|
|
@ -1 +1,2 @@
|
||||||
__pycache__
|
__pycache__
|
||||||
|
.DS_Store
|
||||||
|
|
|
||||||
520
README.md
520
README.md
|
|
@ -2,78 +2,478 @@
|
||||||
|
|
||||||

|

|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
MISP galaxy is a simple method to express a large object called cluster that can be attached to MISP events or
|
MISP galaxy is a simple method to express a large object called cluster that can be attached to MISP events or
|
||||||
attributes. A cluster can be composed of one or more elements. Elements are expressed as key-values. There
|
attributes. A cluster can be composed of one or more elements. Elements are expressed as key-values. There
|
||||||
are default vocabularies available in MISP galaxy but those can be overwritten, replaced or updated as you wish.
|
are default knowledge base (such as Threat Actors, Tools, Ransomware, ATT&CK matrixes) available in MISP galaxy
|
||||||
|
but those can be overwritten, replaced, updated, forked and shared as you wish.
|
||||||
|
|
||||||
Existing clusters and vocabularies can be used as-is or as a template. MISP distribution can be applied
|
Existing clusters and vocabularies can be used as-is or as a common knowledge base. MISP distribution can be applied
|
||||||
to each cluster to permit a limited or broader distribution scheme.
|
to each cluster to permit a limited or broader distribution scheme.
|
||||||
|
|
||||||
Vocabularies are from existing standards (like STIX, Veris, MISP and so on) or custom ones.
|
Galaxies can be also used to expressed existing matrix-like standards such as MITRE ATT&CK(tm) or custom ones.
|
||||||
|
|
||||||
The objective is to have a comment set of clusters for organizations starting analysis but that can be expanded
|
The objective is to have a comment set of clusters for organizations starting analysis but that can be expanded
|
||||||
to localized information (which is not shared) or additional information (that can be shared).
|
to localized information (which is not shared) or additional information (that can be shared).
|
||||||
|
|
||||||
# Available clusters
|
# Available Galaxy - clusters
|
||||||
|
|
||||||
- [clusters/android.json](clusters/android.json) - Android malware galaxy based on multiple open sources.
|
|
||||||
- [clusters/banker.json](clusters/banker.json) - A list of banker malware.
|
|
||||||
- [clusters/stealer.json](clusters/stealer.json) - A list of malware stealer.
|
|
||||||
- [clusters/backdoor.json](clusters/backdoor.json) - A list of backdoor malware.
|
|
||||||
- [clusters/botnet.json](clusters/botnet.json) - A list of known botnets.
|
|
||||||
- [clusters/branded_vulnerability.json](clusters/branded_vulnerability.json) - List of known vulnerabilities and exploits.
|
|
||||||
- [clusters/exploit-kit.json](clusters/exploit-kit.json) - Exploit-Kit is an enumeration of some exploitation kits used by adversaries. The list includes document, browser and router exploit kits. It's not meant to be totally exhaustive but aim at covering the most seen in the past 5 years.
|
|
||||||
- [clusters/microsoft-activity-group.json](clusters/microsoft-activity-group.json) - Activity groups as described by Microsoft.
|
|
||||||
- [clusters/preventive-measure.json](clusters/preventive-measure.json) - Preventive measures.
|
|
||||||
- [clusters/ransomware.json](clusters/ransomware.json) - Ransomware galaxy based on https://docs.google.com/spreadsheets/d/1TWS238xacAto-fLKh1n5uTsdijWdCEsGIM0Y0Hvmc5g/pubhtml
|
|
||||||
- [clusters/rat.json](clusters/rat.json) - remote administration tool or remote access tool (RAT), also called sometimes remote access trojan, is a piece of software or programming that allows a remote "operator" to control a system as if they have physical access to that system.
|
|
||||||
- [clusters/tds.json](clusters/tds.json) - TDS is a list of Traffic Direction System used by adversaries.
|
|
||||||
- [clusters/threat-actor.json](clusters/threat-actor.json) - Adversary groups - Known or estimated adversary groups targeting organizations and employees. Adversary groups are regularly confused with their initial operation or campaign. MISP
|
|
||||||
- [clusters/tool.json](clusters/tool.json) - tool is an enumeration of tools used by adversaries. The list includes malware but also common software regularly used by the adversaries.
|
|
||||||
|
|
||||||
- [clusters/mitre-attack-pattern.json](clusters/mitre-attack-pattern.json) - Attack Pattern - MITRE Adversarial Tactics, Techniques & Common Knowledge (ATT&CK) - v2.0
|
|
||||||
- [clusters/mitre-course-of-action.json](clusters/mitre-course-of-action.json) - Course of Action - MITRE Adversarial Tactics, Techniques & Common Knowledge (ATT&CK) - v2.0
|
|
||||||
- [clusters/mitre-intrusion-set.json](clusters/mitre-intrusion-set.json) - Intrusion Set - MITRE Adversarial Tactics, Techniques & Common Knowledge (ATT&CK) - v2.0
|
|
||||||
- [clusters/mitre-malware.json](clusters/mitre-malware.json) - Malware - MITRE Adversarial Tactics, Techniques & Common Knowledge (ATT&CK) - v2.0
|
|
||||||
- [clusters/mitre-tool.json](clusters/mitre-tool.json) - Tool - MITRE Adversarial Tactics, Techniques & Common Knowledge (ATT&CK) - v2.0
|
|
||||||
|
|
||||||
- [clusters/mitre-ics-assets.json](clusters/mitre-ics-assets.json) - ICS Assets - A list of asset categories that are commonly found in industrial control systems.
|
|
||||||
- [clusters/mitre-ics-groups.json](clusters/mitre-ics-groups.json) - ICS Groups - Groups are sets of related intrusion activity that are tracked by a common name in the security community.
|
|
||||||
- [clusters/mitre-ics-levels.json](clusters/mitre-ics-levels.json) - ICS Levels - Based on the Purdue Model to aid ATT&CK for ICS users to understand which techniques are applicable to their environment.
|
|
||||||
- [clusters/mitre-ics-software.json](clusters/mitre-ics-software.json) - ICS Software - Software is a generic term for custom or commercial code, operating system utilities, open-source software, or other tools used to conduct behavior modeled in ATT&CK for ICS.
|
|
||||||
- [clusters/mitre-ics-tactics.json](clusters/mitre-ics-tactics.json) - ICS Tectics - A list of all tactics in ATT&CK for ICS.
|
|
||||||
- [clusters/mitre-ics-techniques.json](clusters/mitre-ics-techniques.json) - ICS Techniques - A list of Techniques in ATT&CK for ICS.
|
|
||||||
|
|
||||||
- [clusters/sectors.json](clusters/sectors.json) - Activity sectors
|
|
||||||
- [clusters/cert-eu-govsector.json](clusters/cert-eu-govsector.json) - Cert EU GovSector
|
|
||||||
- [clusters/social-dark-patterns.json](clusters/social-dark-patterns.json) - Social Engineering - Dark Patterns
|
|
||||||
|
|
||||||
# Available Vocabularies
|
|
||||||
|
|
||||||
A [readable PDF overview of the MISP galaxy is available](https://www.misp.software/galaxy.pdf) or [HTML](https://www.misp.software/galaxy.html) and generated from the JSON.
|
|
||||||
|
|
||||||
|
|
||||||
## Common
|
|
||||||
|
|
||||||
- [vocabularies/common/certainty-level.json](vocabularies/common/certainty-level.json) - Certainty level of an associated element or cluster.
|
## Android
|
||||||
- [vocabularies/common/threat-actor-type.json](vocabularies/common/threat-actor-type.json) - threat actor type vocab as defined by Cert EU.
|
|
||||||
- [vocabularies/common/ttp-category.json](vocabularies/common/ttp-category.json) - ttp category vocab as defined by Cert EU.
|
[Android](https://www.misp-project.org/galaxy.html#_android) - Android malware galaxy based on multiple open sources.
|
||||||
- [vocabularies/common/ttp-type.json](vocabularies/common/ttp-type.json) - ttp type vocab as defined by Cert EU.
|
|
||||||
|
Category: *tool* - source: *Open Sources* - total: *430* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_android)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/android.json)]
|
||||||
|
|
||||||
|
## attck4fraud
|
||||||
|
|
||||||
|
[attck4fraud](https://www.misp-project.org/galaxy.html#_attck4fraud) - attck4fraud - Principles of MITRE ATT&CK in the fraud domain
|
||||||
|
|
||||||
|
Category: *guidelines* - source: *Open Sources* - total: *31* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_attck4fraud)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/attck4fraud.json)]
|
||||||
|
|
||||||
|
## Backdoor
|
||||||
|
|
||||||
|
[Backdoor](https://www.misp-project.org/galaxy.html#_backdoor) - A list of backdoor malware.
|
||||||
|
|
||||||
|
Category: *tool* - source: *Open Sources* - total: *11* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_backdoor)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/backdoor.json)]
|
||||||
|
|
||||||
|
## Banker
|
||||||
|
|
||||||
|
[Banker](https://www.misp-project.org/galaxy.html#_banker) - A list of banker malware.
|
||||||
|
|
||||||
|
Category: *tool* - source: *Open Sources* - total: *52* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_banker)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/banker.json)]
|
||||||
|
|
||||||
|
## Bhadra Framework
|
||||||
|
|
||||||
|
[Bhadra Framework](https://www.misp-project.org/galaxy.html#_bhadra_framework) - Bhadra Threat Modeling Framework
|
||||||
|
|
||||||
|
Category: *mobile* - source: *https://arxiv.org/pdf/2005.05110.pdf* - total: *47* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_bhadra_framework)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/bhadra-framework.json)]
|
||||||
|
|
||||||
|
## Botnet
|
||||||
|
|
||||||
|
[Botnet](https://www.misp-project.org/galaxy.html#_botnet) - botnet galaxy
|
||||||
|
|
||||||
|
Category: *tool* - source: *MISP Project* - total: *63* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_botnet)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/botnet.json)]
|
||||||
|
|
||||||
|
## Branded Vulnerability
|
||||||
|
|
||||||
|
[Branded Vulnerability](https://www.misp-project.org/galaxy.html#_branded_vulnerability) - List of known vulnerabilities and attacks with a branding
|
||||||
|
|
||||||
|
Category: *vulnerability* - source: *Open Sources* - total: *14* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_branded_vulnerability)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/branded_vulnerability.json)]
|
||||||
|
|
||||||
|
## Cert EU GovSector
|
||||||
|
|
||||||
|
[Cert EU GovSector](https://www.misp-project.org/galaxy.html#_cert_eu_govsector) - Cert EU GovSector
|
||||||
|
|
||||||
|
Category: *sector* - source: *CERT-EU* - total: *6* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_cert_eu_govsector)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/cert-eu-govsector.json)]
|
||||||
|
|
||||||
|
## China Defence Universities Tracker
|
||||||
|
|
||||||
|
[China Defence Universities Tracker](https://www.misp-project.org/galaxy.html#_china_defence_universities_tracker) - The China Defence Universities Tracker is a database of Chinese institutions engaged in military or security-related science and technology research. It was created by ASPI’s International Cyber Policy Centre.
|
||||||
|
|
||||||
|
Category: *academic-institution* - source: *ASPI International Cyber Policy Centre* - total: *159* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_china_defence_universities_tracker)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/china-defence-universities.json)]
|
||||||
|
|
||||||
|
## CONCORDIA Mobile Modelling Framework - Attack Pattern
|
||||||
|
|
||||||
|
[CONCORDIA Mobile Modelling Framework - Attack Pattern](https://www.misp-project.org/galaxy.html#_concordia_mobile_modelling_framework_-_attack_pattern) - A list of Techniques in CONCORDIA Mobile Modelling Framework.
|
||||||
|
|
||||||
|
Category: *cmtmf-attack-pattern* - source: *https://5g4iot.vlab.cs.hioa.no/* - total: *93* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_concordia_mobile_modelling_framework_-_attack_pattern)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/cmtmf-attack-pattern.json)]
|
||||||
|
|
||||||
|
## Country
|
||||||
|
|
||||||
|
[Country](https://www.misp-project.org/galaxy.html#_country) - Country meta information based on the database provided by geonames.org.
|
||||||
|
|
||||||
|
Category: *country* - source: *MISP Project* - total: *252* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_country)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/country.json)]
|
||||||
|
|
||||||
|
## Cryptominers
|
||||||
|
|
||||||
|
[Cryptominers](https://www.misp-project.org/galaxy.html#_cryptominers) - A list of cryptominer and cryptojacker malware.
|
||||||
|
|
||||||
|
Category: *Cryptominers* - source: *Open Source Intelligence* - total: *2* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_cryptominers)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/cryptominers.json)]
|
||||||
|
|
||||||
|
## Election guidelines
|
||||||
|
|
||||||
|
[Election guidelines](https://www.misp-project.org/galaxy.html#_election_guidelines) - Universal Development and Security Guidelines as Applicable to Election Technology.
|
||||||
|
|
||||||
|
Category: *guidelines* - source: *Open Sources* - total: *23* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_election_guidelines)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/election-guidelines.json)]
|
||||||
|
|
||||||
|
## Exploit-Kit
|
||||||
|
|
||||||
|
[Exploit-Kit](https://www.misp-project.org/galaxy.html#_exploit-kit) - Exploit-Kit is an enumeration of some exploitation kits used by adversaries. The list includes document, browser and router exploit kits.It's not meant to be totally exhaustive but aim at covering the most seen in the past 5 years
|
||||||
|
|
||||||
|
Category: *tool* - source: *MISP Project* - total: *52* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_exploit-kit)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/exploit-kit.json)]
|
||||||
|
|
||||||
|
## Malpedia
|
||||||
|
|
||||||
|
[Malpedia](https://www.misp-project.org/galaxy.html#_malpedia) - Malware galaxy cluster based on Malpedia.
|
||||||
|
|
||||||
|
Category: *tool* - source: *Malpedia* - total: *2194* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_malpedia)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/malpedia.json)]
|
||||||
|
|
||||||
|
## Microsoft Activity Group actor
|
||||||
|
|
||||||
|
[Microsoft Activity Group actor](https://www.misp-project.org/galaxy.html#_microsoft_activity_group_actor) - Activity groups as described by Microsoft
|
||||||
|
|
||||||
|
Category: *actor* - source: *MISP Project* - total: *15* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_microsoft_activity_group_actor)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/microsoft-activity-group.json)]
|
||||||
|
|
||||||
|
## Misinformation Pattern
|
||||||
|
|
||||||
|
[Misinformation Pattern](https://www.misp-project.org/galaxy.html#_misinformation_pattern) - AM!TT Technique
|
||||||
|
|
||||||
|
Category: *misinformation-pattern* - source: *https://github.com/misinfosecproject/amitt_framework* - total: *61* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_misinformation_pattern)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/misinfosec-amitt-misinformation-pattern.json)]
|
||||||
|
|
||||||
|
## Attack Pattern
|
||||||
|
|
||||||
|
[Attack Pattern](https://www.misp-project.org/galaxy.html#_attack_pattern) - ATT&CK tactic
|
||||||
|
|
||||||
|
Category: *attack-pattern* - source: *https://github.com/mitre/cti* - total: *991* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_attack_pattern)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/mitre-attack-pattern.json)]
|
||||||
|
|
||||||
|
## Course of Action
|
||||||
|
|
||||||
|
[Course of Action](https://www.misp-project.org/galaxy.html#_course_of_action) - ATT&CK Mitigation
|
||||||
|
|
||||||
|
Category: *course-of-action* - source: *https://github.com/mitre/cti* - total: *279* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_course_of_action)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/mitre-course-of-action.json)]
|
||||||
|
|
||||||
|
## Enterprise Attack - Attack Pattern
|
||||||
|
|
||||||
|
[Enterprise Attack - Attack Pattern](https://www.misp-project.org/galaxy.html#_enterprise_attack_-_attack_pattern) - ATT&CK tactic
|
||||||
|
|
||||||
|
Category: *attack-pattern* - source: *https://github.com/mitre/cti* - total: *219* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_enterprise_attack_-_attack_pattern)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/mitre-enterprise-attack-attack-pattern.json)]
|
||||||
|
|
||||||
|
## Enterprise Attack - Course of Action
|
||||||
|
|
||||||
|
[Enterprise Attack - Course of Action](https://www.misp-project.org/galaxy.html#_enterprise_attack_-_course_of_action) - ATT&CK Mitigation
|
||||||
|
|
||||||
|
Category: *course-of-action* - source: *https://github.com/mitre/cti* - total: *215* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_enterprise_attack_-_course_of_action)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/mitre-enterprise-attack-course-of-action.json)]
|
||||||
|
|
||||||
|
## Enterprise Attack - Intrusion Set
|
||||||
|
|
||||||
|
[Enterprise Attack - Intrusion Set](https://www.misp-project.org/galaxy.html#_enterprise_attack_-_intrusion_set) - Name of ATT&CK Group
|
||||||
|
|
||||||
|
Category: *actor* - source: *https://github.com/mitre/cti* - total: *69* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_enterprise_attack_-_intrusion_set)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/mitre-enterprise-attack-intrusion-set.json)]
|
||||||
|
|
||||||
|
## Enterprise Attack - Malware
|
||||||
|
|
||||||
|
[Enterprise Attack - Malware](https://www.misp-project.org/galaxy.html#_enterprise_attack_-_malware) - Name of ATT&CK software
|
||||||
|
|
||||||
|
Category: *tool* - source: *https://github.com/mitre/cti* - total: *188* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_enterprise_attack_-_malware)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/mitre-enterprise-attack-malware.json)]
|
||||||
|
|
||||||
|
## Enterprise Attack - Tool
|
||||||
|
|
||||||
|
[Enterprise Attack - Tool](https://www.misp-project.org/galaxy.html#_enterprise_attack_-_tool) - Name of ATT&CK software
|
||||||
|
|
||||||
|
Category: *tool* - source: *https://github.com/mitre/cti* - total: *45* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_enterprise_attack_-_tool)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/mitre-enterprise-attack-tool.json)]
|
||||||
|
|
||||||
|
## Assets
|
||||||
|
|
||||||
|
[Assets](https://www.misp-project.org/galaxy.html#_assets) - A list of asset categories that are commonly found in industrial control systems.
|
||||||
|
|
||||||
|
Category: *asset* - source: *https://collaborate.mitre.org/attackics/index.php/All_Assets* - total: *7* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_assets)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/mitre-ics-assets.json)]
|
||||||
|
|
||||||
|
## Groups
|
||||||
|
|
||||||
|
[Groups](https://www.misp-project.org/galaxy.html#_groups) - Groups are sets of related intrusion activity that are tracked by a common name in the security community. Groups are also sometimes referred to as campaigns or intrusion sets. Some groups have multiple names associated with the same set of activities due to various organizations tracking the same set of activities by different names. Groups are mapped to publicly reported technique use and referenced in the ATT&CK for ICS knowledge base. Groups are also mapped to reported software used during intrusions.
|
||||||
|
|
||||||
|
Category: *actor* - source: *https://collaborate.mitre.org/attackics/index.php/Groups* - total: *10* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_groups)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/mitre-ics-groups.json)]
|
||||||
|
|
||||||
|
## Levels
|
||||||
|
|
||||||
|
[Levels](https://www.misp-project.org/galaxy.html#_levels) - Based on the Purdue Model to aid ATT&CK for ICS users to understand which techniques are applicable to their environment.
|
||||||
|
|
||||||
|
Category: *level* - source: *https://collaborate.mitre.org/attackics/index.php/All_Levels* - total: *3* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_levels)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/mitre-ics-levels.json)]
|
||||||
|
|
||||||
|
## Software
|
||||||
|
|
||||||
|
[Software](https://www.misp-project.org/galaxy.html#_software) - Software is a generic term for custom or commercial code, operating system utilities, open-source software, or other tools used to conduct behavior modeled in ATT&CK for ICS.
|
||||||
|
|
||||||
|
Category: *tool* - source: *https://collaborate.mitre.org/attackics/index.php/Software* - total: *17* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_software)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/mitre-ics-software.json)]
|
||||||
|
|
||||||
|
## Tactics
|
||||||
|
|
||||||
|
[Tactics](https://www.misp-project.org/galaxy.html#_tactics) - A list of all 11 tactics in ATT&CK for ICS
|
||||||
|
|
||||||
|
Category: *tactic* - source: *https://collaborate.mitre.org/attackics/index.php/All_Tactics* - total: *9* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_tactics)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/mitre-ics-tactics.json)]
|
||||||
|
|
||||||
|
## Techniques
|
||||||
|
|
||||||
|
[Techniques](https://www.misp-project.org/galaxy.html#_techniques) - A list of Techniques in ATT&CK for ICS.
|
||||||
|
|
||||||
|
Category: *attack-pattern* - source: *https://collaborate.mitre.org/attackics/index.php/All_Techniques* - total: *78* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_techniques)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/mitre-ics-techniques.json)]
|
||||||
|
|
||||||
|
## Intrusion Set
|
||||||
|
|
||||||
|
[Intrusion Set](https://www.misp-project.org/galaxy.html#_intrusion_set) - Name of ATT&CK Group
|
||||||
|
|
||||||
|
Category: *actor* - source: *https://github.com/mitre/cti* - total: *134* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_intrusion_set)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/mitre-intrusion-set.json)]
|
||||||
|
|
||||||
|
## Malware
|
||||||
|
|
||||||
|
[Malware](https://www.misp-project.org/galaxy.html#_malware) - Name of ATT&CK software
|
||||||
|
|
||||||
|
Category: *tool* - source: *https://github.com/mitre/cti* - total: *565* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_malware)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/mitre-malware.json)]
|
||||||
|
|
||||||
|
## Mobile Attack - Attack Pattern
|
||||||
|
|
||||||
|
[Mobile Attack - Attack Pattern](https://www.misp-project.org/galaxy.html#_mobile_attack_-_attack_pattern) - ATT&CK tactic
|
||||||
|
|
||||||
|
Category: *attack-pattern* - source: *https://github.com/mitre/cti* - total: *76* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_mobile_attack_-_attack_pattern)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/mitre-mobile-attack-attack-pattern.json)]
|
||||||
|
|
||||||
|
## Mobile Attack - Course of Action
|
||||||
|
|
||||||
|
[Mobile Attack - Course of Action](https://www.misp-project.org/galaxy.html#_mobile_attack_-_course_of_action) - ATT&CK Mitigation
|
||||||
|
|
||||||
|
Category: *course-of-action* - source: *https://github.com/mitre/cti* - total: *14* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_mobile_attack_-_course_of_action)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/mitre-mobile-attack-course-of-action.json)]
|
||||||
|
|
||||||
|
## Mobile Attack - Intrusion Set
|
||||||
|
|
||||||
|
[Mobile Attack - Intrusion Set](https://www.misp-project.org/galaxy.html#_mobile_attack_-_intrusion_set) - Name of ATT&CK Group
|
||||||
|
|
||||||
|
Category: *actor* - source: *https://github.com/mitre/cti* - total: *1* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_mobile_attack_-_intrusion_set)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/mitre-mobile-attack-intrusion-set.json)]
|
||||||
|
|
||||||
|
## Mobile Attack - Malware
|
||||||
|
|
||||||
|
[Mobile Attack - Malware](https://www.misp-project.org/galaxy.html#_mobile_attack_-_malware) - Name of ATT&CK software
|
||||||
|
|
||||||
|
Category: *tool* - source: *https://github.com/mitre/cti* - total: *35* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_mobile_attack_-_malware)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/mitre-mobile-attack-malware.json)]
|
||||||
|
|
||||||
|
## Mobile Attack - Tool
|
||||||
|
|
||||||
|
[Mobile Attack - Tool](https://www.misp-project.org/galaxy.html#_mobile_attack_-_tool) - Name of ATT&CK software
|
||||||
|
|
||||||
|
Category: *tool* - source: *https://github.com/mitre/cti* - total: *1* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_mobile_attack_-_tool)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/mitre-mobile-attack-tool.json)]
|
||||||
|
|
||||||
|
## Pre Attack - Attack Pattern
|
||||||
|
|
||||||
|
[Pre Attack - Attack Pattern](https://www.misp-project.org/galaxy.html#_pre_attack_-_attack_pattern) - ATT&CK tactic
|
||||||
|
|
||||||
|
Category: *attack-pattern* - source: *https://github.com/mitre/cti* - total: *174* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_pre_attack_-_attack_pattern)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/mitre-pre-attack-attack-pattern.json)]
|
||||||
|
|
||||||
|
## Pre Attack - Intrusion Set
|
||||||
|
|
||||||
|
[Pre Attack - Intrusion Set](https://www.misp-project.org/galaxy.html#_pre_attack_-_intrusion_set) - Name of ATT&CK Group
|
||||||
|
|
||||||
|
Category: *actor* - source: *https://github.com/mitre/cti* - total: *7* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_pre_attack_-_intrusion_set)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/mitre-pre-attack-intrusion-set.json)]
|
||||||
|
|
||||||
|
## Tool
|
||||||
|
|
||||||
|
[Tool](https://www.misp-project.org/galaxy.html#_tool) - Name of ATT&CK software
|
||||||
|
|
||||||
|
Category: *tool* - source: *https://github.com/mitre/cti* - total: *74* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_tool)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/mitre-tool.json)]
|
||||||
|
|
||||||
|
## o365-exchange-techniques
|
||||||
|
|
||||||
|
[o365-exchange-techniques](https://www.misp-project.org/galaxy.html#_o365-exchange-techniques) - o365-exchange-techniques - Office365/Exchange related techniques by @johnLaTwC and @inversecos
|
||||||
|
|
||||||
|
Category: *guidelines* - source: *Open Sources, https://www.inversecos.com/2021/09/office365-attacks-bypassing-mfa.html* - total: *62* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_o365-exchange-techniques)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/o365-exchange-techniques.json)]
|
||||||
|
|
||||||
|
## Preventive Measure
|
||||||
|
|
||||||
|
[Preventive Measure](https://www.misp-project.org/galaxy.html#_preventive_measure) - Preventive measures based on the ransomware document overview as published in https://docs.google.com/spreadsheets/d/1TWS238xacAto-fLKh1n5uTsdijWdCEsGIM0Y0Hvmc5g/pubhtml# . The preventive measures are quite generic and can fit any standard Windows infrastructure and their security measures.
|
||||||
|
|
||||||
|
Category: *measure* - source: *MISP Project* - total: *20* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_preventive_measure)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/preventive-measure.json)]
|
||||||
|
|
||||||
|
## Ransomware
|
||||||
|
|
||||||
|
[Ransomware](https://www.misp-project.org/galaxy.html#_ransomware) - Ransomware galaxy based on https://docs.google.com/spreadsheets/d/1TWS238xacAto-fLKh1n5uTsdijWdCEsGIM0Y0Hvmc5g/pubhtml and http://pastebin.com/raw/GHgpWjar
|
||||||
|
|
||||||
|
Category: *tool* - source: *Various* - total: *1602* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_ransomware)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/ransomware.json)]
|
||||||
|
|
||||||
|
## RAT
|
||||||
|
|
||||||
|
[RAT](https://www.misp-project.org/galaxy.html#_rat) - remote administration tool or remote access tool (RAT), also called sometimes remote access trojan, is a piece of software or programming that allows a remote "operator" to control a system as if they have physical access to that system.
|
||||||
|
|
||||||
|
Category: *tool* - source: *MISP Project* - total: *262* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_rat)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/rat.json)]
|
||||||
|
|
||||||
|
## Regions UN M49
|
||||||
|
|
||||||
|
[Regions UN M49](https://www.misp-project.org/galaxy.html#_regions_un_m49) - Regions based on UN M49.
|
||||||
|
|
||||||
|
Category: *location* - source: *https://unstats.un.org/unsd/methodology/m49/overview/* - total: *31* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_regions_un_m49)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/region.json)]
|
||||||
|
|
||||||
|
## rsit
|
||||||
|
|
||||||
|
[rsit](https://www.misp-project.org/galaxy.html#_rsit) - rsit
|
||||||
|
|
||||||
|
Category: *rsit* - source: *https://github.com/enisaeu/Reference-Security-Incident-Taxonomy-Task-Force* - total: *39* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_rsit)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/rsit.json)]
|
||||||
|
|
||||||
|
## Sector
|
||||||
|
|
||||||
|
[Sector](https://www.misp-project.org/galaxy.html#_sector) - Activity sectors
|
||||||
|
|
||||||
|
Category: *sector* - source: *CERT-EU* - total: *117* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_sector)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/sector.json)]
|
||||||
|
|
||||||
|
## Dark Patterns
|
||||||
|
|
||||||
|
[Dark Patterns](https://www.misp-project.org/galaxy.html#_dark_patterns) - Dark Patterns are user interface that tricks users into making decisions that benefit the interface's holder to the expense of the user.
|
||||||
|
|
||||||
|
Category: *dark-patterns* - source: *CIRCL* - total: *19* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_dark_patterns)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/social-dark-patterns.json)]
|
||||||
|
|
||||||
|
## SoD Matrix
|
||||||
|
|
||||||
|
[SoD Matrix](https://www.misp-project.org/galaxy.html#_sod_matrix) - SOD Matrix
|
||||||
|
|
||||||
|
Category: *sod-matrix* - source: *https://github.com/cudeso/SoD-Matrix* - total: *276* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_sod_matrix)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/sod-matrix.json)]
|
||||||
|
|
||||||
|
## Stealer
|
||||||
|
|
||||||
|
[Stealer](https://www.misp-project.org/galaxy.html#_stealer) - A list of malware stealer.
|
||||||
|
|
||||||
|
Category: *tool* - source: *Open Sources* - total: *6* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_stealer)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/stealer.json)]
|
||||||
|
|
||||||
|
## Surveillance Vendor
|
||||||
|
|
||||||
|
[Surveillance Vendor](https://www.misp-project.org/galaxy.html#_surveillance_vendor) - List of vendors selling surveillance technologies including malware, interception devices or computer exploitation services.
|
||||||
|
|
||||||
|
Category: *actor* - source: *MISP Project* - total: *13* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_surveillance_vendor)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/surveillance-vendor.json)]
|
||||||
|
|
||||||
|
## Target Information
|
||||||
|
|
||||||
|
[Target Information](https://www.misp-project.org/galaxy.html#_target_information) - Description of targets of threat actors.
|
||||||
|
|
||||||
|
Category: *target* - source: *Various* - total: *240* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_target_information)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/target-information.json)]
|
||||||
|
|
||||||
|
## TDS
|
||||||
|
|
||||||
|
[TDS](https://www.misp-project.org/galaxy.html#_tds) - TDS is a list of Traffic Direction System used by adversaries
|
||||||
|
|
||||||
|
Category: *tool* - source: *MISP Project* - total: *10* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_tds)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/tds.json)]
|
||||||
|
|
||||||
|
## Tea Matrix
|
||||||
|
|
||||||
|
[Tea Matrix](https://www.misp-project.org/galaxy.html#_tea_matrix) - Tea Matrix
|
||||||
|
|
||||||
|
Category: *tea-matrix* - source: ** - total: *7* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_tea_matrix)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/tea-matrix.json)]
|
||||||
|
|
||||||
## Threat Actor
|
## Threat Actor
|
||||||
|
|
||||||
- [vocabularies/threat-actor/cert-eu-motive.json](vocabularies/threat-actor/cert-eu-motive.json) - Motive vocab as defined by Cert EU.
|
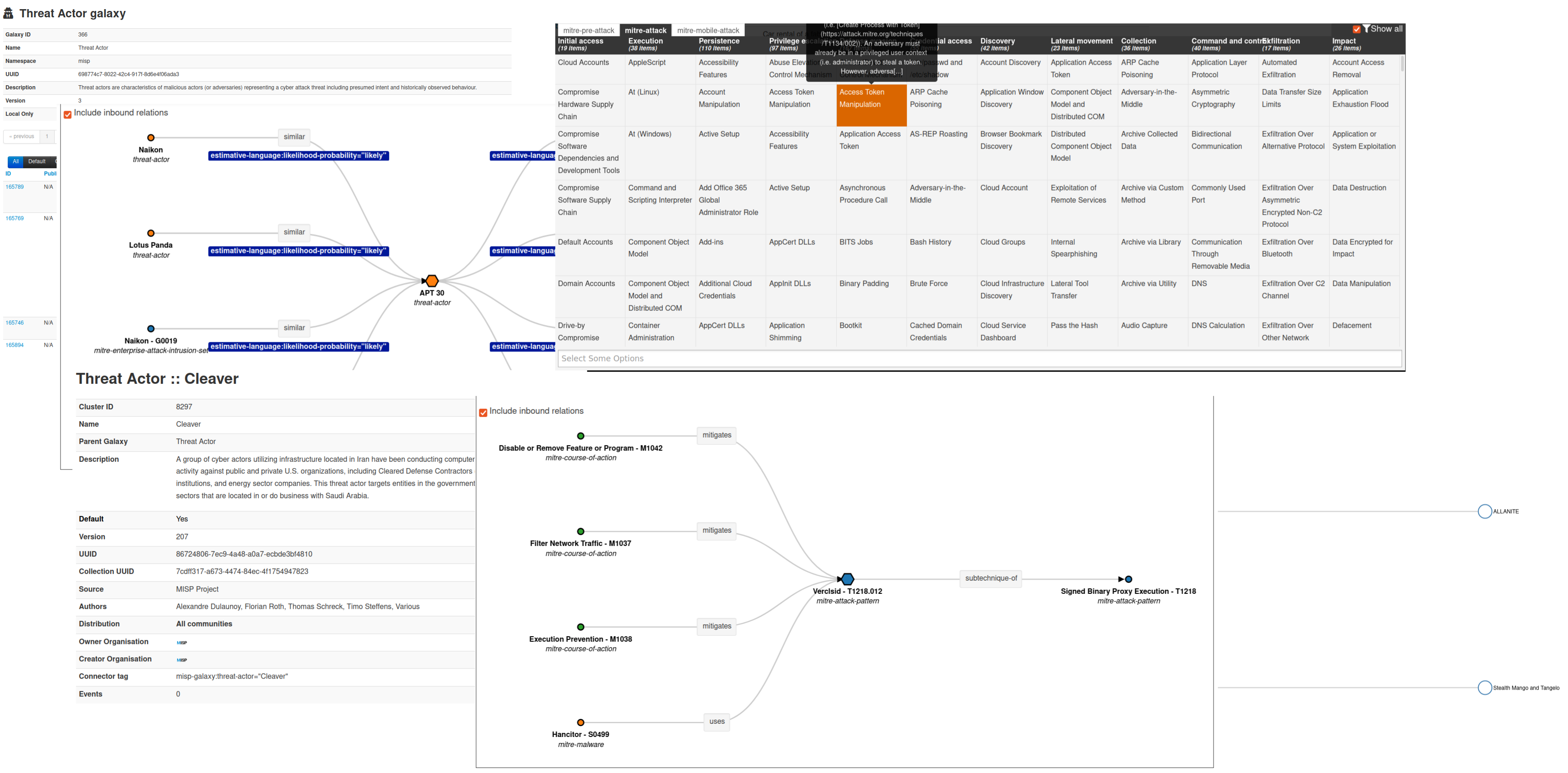
[Threat Actor](https://www.misp-project.org/galaxy.html#_threat_actor) - Known or estimated adversary groups targeting organizations and employees. Adversary groups are regularly confused with their initial operation or campaign. threat-actor-classification meta can be used to clarify the understanding of the threat-actor if also considered as operation, campaign or activity group.
|
||||||
- [vocabularies/threat-actor/intended-effect-vocabulary.json](vocabularies/threat-actor/intended-effect.json) - The IntendedEffectVocab is the default STIX vocabulary for expressing the intended effect of a threat actor. STIX 1.2.1
|
|
||||||
- [vocabularies/threat-actor/motivation-vocabulary.json](vocabularies/threat-actor/motivation.json) - The MotivationVocab is the default STIX vocabulary for expressing the motivation of a threat actor. STIX 1.2.1
|
|
||||||
- [vocabularies/threat-actor/planning-and-operational-support-vocabulary.json](vocabularies/threat-actor/planning-and-operational-support.json) - The PlanningAndOperationalSupportVocab is the default STIX vocabulary for expressing the planning and operational support functions available to a threat actor.
|
|
||||||
- [vocabularies/threat-actor/sophistication.json](vocabularies/threat-actor/sophistication.json) - The ThreatActorSophisticationVocab enumeration is used to define the default STIX vocabulary for expressing the subjective level of sophistication of a threat actor.
|
|
||||||
- [vocabularies/threat-actor/type.json](vocabularies/threat-actor/type.json) - The ThreatActorTypeVocab enumeration is used to define the default STIX vocabulary for expressing the subjective type of a threat actor.
|
|
||||||
|
|
||||||
## MISP Integration
|
Category: *actor* - source: *MISP Project* - total: *366* elements
|
||||||
|
|
||||||
Starting from [MISP 2.4.56](http://www.misp-project.org/2016/12/07/MISP.2.4.56.released.html), galaxy is integrated within the MISP threat sharing platform and users can directly benefit from the available clusters to attach them to the MISP event.
|
[[HTML](https://www.misp-project.org/galaxy.html#_threat_actor)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/threat-actor.json)]
|
||||||
|
|
||||||
|
## Tool
|
||||||
|
|
||||||
|
[Tool](https://www.misp-project.org/galaxy.html#_tool) - threat-actor-tools is an enumeration of tools used by adversaries. The list includes malware but also common software regularly used by the adversaries.
|
||||||
|
|
||||||
|
Category: *tool* - source: *MISP Project* - total: *530* elements
|
||||||
|
|
||||||
|
[[HTML](https://www.misp-project.org/galaxy.html#_tool)] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/tool.json)]
|
||||||
|
|
||||||
|
|
||||||
|
# Online documentation
|
||||||
|
|
||||||
|
A [readable PDF overview of the MISP galaxy is available](https://www.misp.software/galaxy.pdf) or [HTML](https://www.misp.software/galaxy.html) and generated from the JSON.
|
||||||
|
|
||||||

|
|
||||||
## How to contribute?
|
## How to contribute?
|
||||||
|
|
||||||
- [Read the contribution document](CONTRIBUTE.md)
|
- [Read the contribution document](CONTRIBUTE.md)
|
||||||
|
|
@ -87,12 +487,12 @@ The MISP galaxy (JSON files) are dual-licensed under:
|
||||||
or
|
or
|
||||||
|
|
||||||
~~~~
|
~~~~
|
||||||
Copyright (c) 2015-2019 Alexandre Dulaunoy - a@foo.be
|
Copyright (c) 2015-2022 Alexandre Dulaunoy - a@foo.be
|
||||||
Copyright (c) 2015-2019 CIRCL - Computer Incident Response Center Luxembourg
|
Copyright (c) 2015-2022 CIRCL - Computer Incident Response Center Luxembourg
|
||||||
Copyright (c) 2015-2019 Andras Iklody
|
Copyright (c) 2015-2022 Andras Iklody
|
||||||
Copyright (c) 2015-2019 Raphael Vinot
|
Copyright (c) 2015-2022 Raphael Vinot
|
||||||
Copyright (c) 2015-2019 Deborah Servili
|
Copyright (c) 2015-2022 Deborah Servili
|
||||||
Copyright (c) 2016-2019 Various contributors to MISP Project
|
Copyright (c) 2016-2022 Various contributors to MISP Project
|
||||||
|
|
||||||
Redistribution and use in source and binary forms, with or without modification,
|
Redistribution and use in source and binary forms, with or without modification,
|
||||||
are permitted provided that the following conditions are met:
|
are permitted provided that the following conditions are met:
|
||||||
|
|
|
||||||
|
|
@ -1181,7 +1181,23 @@
|
||||||
},
|
},
|
||||||
"uuid": "ea2906a5-d493-4afa-b770-436c0c246c78",
|
"uuid": "ea2906a5-d493-4afa-b770-436c0c246c78",
|
||||||
"value": "Mozi"
|
"value": "Mozi"
|
||||||
|
},
|
||||||
|
{
|
||||||
|
"description": "UPAS-Kit was advertised by auroras a/k/a vinny in middle of june 2012 via exploit.in. Upas is the predecessor of Kronos. Marcus Hutchins helped create and, in partnership with another, sell malicious computer code, a/k/a malware, known as UPAS-Kit.",
|
||||||
|
"meta": {
|
||||||
|
"refs": [
|
||||||
|
"https://research.checkpoint.com/2018/deep-dive-upas-kit-vs-kronos/",
|
||||||
|
"https://malware.dontneedcoffee.com/2012/08/inside-upas-kit1.0.1.1.html",
|
||||||
|
"https://web.archive.org/web/20130120062602/http://onthar.in/articles/upas-kit-analysis/",
|
||||||
|
"https://regmedia.co.uk/2019/04/19/plea.pdf"
|
||||||
|
],
|
||||||
|
"synonyms": [
|
||||||
|
"Rombrast"
|
||||||
|
]
|
||||||
|
},
|
||||||
|
"uuid": "099223a1-4a6e-4024-8e48-dbe199ec7244",
|
||||||
|
"value": "UPAS-Kit"
|
||||||
}
|
}
|
||||||
],
|
],
|
||||||
"version": 22
|
"version": 23
|
||||||
}
|
}
|
||||||
|
|
|
||||||
1050
clusters/cmtmf-attack-pattern.json
Normal file
1050
clusters/cmtmf-attack-pattern.json
Normal file
File diff suppressed because it is too large
Load diff
|
|
@ -3499,7 +3499,37 @@
|
||||||
},
|
},
|
||||||
"uuid": "a5e5a48a-5ce7-45f0-97d7-517d7f37b4ce",
|
"uuid": "a5e5a48a-5ce7-45f0-97d7-517d7f37b4ce",
|
||||||
"value": "Milan"
|
"value": "Milan"
|
||||||
|
},
|
||||||
|
{
|
||||||
|
"description": "In late November, Prevailion’s Adversarial Counterintelligence Team (PACT) identified what appeared to be a malicious javascript-based Remote Access Trojan (RAT) that uses a robust Domain Generation Algorithm (DGA) to identify its Command and Control (C2) infrastructure and that utilizes novel methods for fileless persistence, on-system activity, and dynamic run-time capabilities like self-updating and recompilation. This RAT, which PACT refers to by its internal codename “DarkWatchman”, has been observed being distributed by email and represents an evolution in fileless malware techniques, as it uses the registry for nearly all temporary and permanent storage and therefore never writes anything to disk, allowing it to operate beneath or around the detection threshold of most security tools. PACT has reverse engineered the DGA, dynamically analyzed the malware, investigated the Threat Actor’s (TA) web-based infrastructure, and consolidated the results of our analysis into the following report.",
|
||||||
|
"meta": {
|
||||||
|
"refs": [
|
||||||
|
"https://www.prevailion.com/darkwatchman-new-fileness-techniques/"
|
||||||
|
],
|
||||||
|
"synonyms": []
|
||||||
|
},
|
||||||
|
"uuid": "35198ca6-6f8d-49cd-be1b-65f21b2e7e00",
|
||||||
|
"value": "DarkWatchman"
|
||||||
|
},
|
||||||
|
{
|
||||||
|
"description": "Malwarebytes Lab identified a new variant of the BADNEWS RAT called Ragnatela. It is being distributed via spear phishing emails to targets of interest in Pakistan. Ragnatela, which means spider web in Italian, is also the project name and panel used by Patchwork APT. Ironically, the threat actor infected themselves with their own RAT.",
|
||||||
|
"meta": {
|
||||||
|
"refs": [
|
||||||
|
"https://blog.malwarebytes.com/threat-intelligence/2022/01/patchwork-apt-caught-in-its-own-web/"
|
||||||
|
]
|
||||||
|
},
|
||||||
|
"related": [
|
||||||
|
{
|
||||||
|
"dest-uuid": "e9595678-d269-469e-ae6b-75e49259de63",
|
||||||
|
"tags": [
|
||||||
|
"estimative-language:likelihood-probability=\"likely\""
|
||||||
|
],
|
||||||
|
"type": "similar"
|
||||||
}
|
}
|
||||||
],
|
],
|
||||||
"version": 37
|
"uuid": "e79cb167-6639-46a3-9646-b12535aa21b6",
|
||||||
|
"value": "Ragnatela"
|
||||||
|
}
|
||||||
|
],
|
||||||
|
"version": 38
|
||||||
}
|
}
|
||||||
|
|
|
||||||
|
|
@ -8879,7 +8879,43 @@
|
||||||
},
|
},
|
||||||
"uuid": "da581c60-7c3d-4de6-b54c-cafea1c58389",
|
"uuid": "da581c60-7c3d-4de6-b54c-cafea1c58389",
|
||||||
"value": "Common Raven"
|
"value": "Common Raven"
|
||||||
|
},
|
||||||
|
{
|
||||||
|
"description": "Since 2017, Mandiant has been tracking FIN13, an industrious and versatile financially motivated threat actor conducting long-term intrusions in Mexico with an activity timeframe stretching back as early as 2016. Although their operations continue through the present day, in many ways FIN13's intrusions are like a time capsule of traditional financial cybercrime from days past. Instead of today's prevalent smash-and-grab ransomware groups, FIN13 takes their time to gather information to perform fraudulent money transfers. Rather than relying heavily on attack frameworks such as Cobalt Strike, the majority of FIN13 intrusions involve heavy use of custom passive backdoors and tools to lurk in environments for the long haul.",
|
||||||
|
"meta": {
|
||||||
|
"refs": [
|
||||||
|
"https://www.mandiant.com/resources/fin13-cybercriminal-mexico"
|
||||||
|
]
|
||||||
|
},
|
||||||
|
"uuid": "60fa684d-c738-4b77-98fb-3f6605e2bb82",
|
||||||
|
"value": "FIN13"
|
||||||
|
},
|
||||||
|
{
|
||||||
|
"description": "The SideCopy APT is a Pakistani threat actor that has been operating since at least 2019, mainly targeting South Asian countries and more specifically India and Afghanistan. Its name comes from its infection chain that tries to mimic that of the SideWinder APT. It has been reported that this actor has similarities with Transparent Tribe (APT36) and possibly is a subdivision of this actor. Cisco Talos and Seqrite have provided comprehensive reports on this actor’s activities.",
|
||||||
|
"meta": {
|
||||||
|
"country": "PK",
|
||||||
|
"refs": [
|
||||||
|
"https://www.seqrite.com/blog/operation-sidecopy/",
|
||||||
|
"https://blog.malwarebytes.com/threat-intelligence/2021/12/sidecopy-apt-connecting-lures-to-victims-payloads-to-infrastructure/",
|
||||||
|
"https://www.telsy.com/sidecopy-apt-from-windows-to-nix/",
|
||||||
|
"https://blog.talosintelligence.com/2021/07/sidecopy.html",
|
||||||
|
"https://about.fb.com/news/2021/11/taking-action-against-hackers-in-pakistan-and-syria/"
|
||||||
|
]
|
||||||
|
},
|
||||||
|
"uuid": "f6d02ac3-3447-4892-b844-1ef31839e04f",
|
||||||
|
"value": "SideCopy"
|
||||||
|
},
|
||||||
|
{
|
||||||
|
"description": "AQUATIC PANDA is a China-based targeted intrusion adversary with a dual mission of intelligence collection and industrial espionage. It has likely operated since at least May 2020. AQUATIC PANDA operations have primarily focused on entities in the telecommunications, technology and government sectors. AQUATIC PANDA relies heavily on Cobalt Strike, and its toolset includes the unique Cobalt Strike downloader tracked as FishMaster. AQUATIC PANDA has also been observed delivering njRAT payloads to targets.",
|
||||||
|
"meta": {
|
||||||
|
"country": "CN",
|
||||||
|
"refs": [
|
||||||
|
"https://www.crowdstrike.com/blog/overwatch-exposes-aquatic-panda-in-possession-of-log-4-shell-exploit-tools/"
|
||||||
|
]
|
||||||
|
},
|
||||||
|
"uuid": "676c1129-5664-4698-92ee-031f81baefce",
|
||||||
|
"value": "AQUATIC PANDA"
|
||||||
}
|
}
|
||||||
],
|
],
|
||||||
"version": 208
|
"version": 210
|
||||||
}
|
}
|
||||||
|
|
|
||||||
|
|
@ -8460,6 +8460,17 @@
|
||||||
},
|
},
|
||||||
"uuid": "9ea6d29e-00a7-4042-9bc5-31b1adeee6ec",
|
"uuid": "9ea6d29e-00a7-4042-9bc5-31b1adeee6ec",
|
||||||
"value": "Shark"
|
"value": "Shark"
|
||||||
|
},
|
||||||
|
{
|
||||||
|
"description": "Motnug is a simple shellcode loader that is used to load and execute shellcode located either in its overlay or in a separate file stored on disk.",
|
||||||
|
"meta": {
|
||||||
|
"refs": [
|
||||||
|
"https://www.welivesecurity.com/2021/08/24/sidewalk-may-be-as-dangerous-as-crosswalk/",
|
||||||
|
"https://www.welivesecurity.com/2021/09/23/famoussparrow-suspicious-hotel-guest/"
|
||||||
|
]
|
||||||
|
},
|
||||||
|
"uuid": "f3bae23a-ec73-49cb-8149-f93578bb2bff",
|
||||||
|
"value": "Motnug"
|
||||||
}
|
}
|
||||||
],
|
],
|
||||||
"version": 149
|
"version": 149
|
||||||
|
|
|
||||||
BIN
doc/images/galaxy.png
Normal file
BIN
doc/images/galaxy.png
Normal file
Binary file not shown.
|
After Width: | Height: | Size: 980 KiB |
27
galaxies/cmtmf-attack-pattern.json
Normal file
27
galaxies/cmtmf-attack-pattern.json
Normal file
|
|
@ -0,0 +1,27 @@
|
||||||
|
{
|
||||||
|
"description": "CONCORDIA Mobile Modeling Framework - Tactics",
|
||||||
|
"icon": "mobile",
|
||||||
|
"kill_chain_order": {
|
||||||
|
"cmtmf-attack": [
|
||||||
|
"reconnaissance",
|
||||||
|
"resource-development",
|
||||||
|
"initial-access",
|
||||||
|
"execution",
|
||||||
|
"persistence",
|
||||||
|
"privilege-escalation",
|
||||||
|
"defense-evasion",
|
||||||
|
"credential-access",
|
||||||
|
"discovery",
|
||||||
|
"lateral-movement",
|
||||||
|
"collection",
|
||||||
|
"command-and-control",
|
||||||
|
"exfiltration",
|
||||||
|
"impact"
|
||||||
|
]
|
||||||
|
},
|
||||||
|
"name": "CONCORDIA Mobile Modelling Framework - Attack Pattern",
|
||||||
|
"namespace": "cmmf-attack",
|
||||||
|
"type": "cmtmf-attack-pattern",
|
||||||
|
"uuid": "51060d01-ef29-40ab-8965-8031d0941811",
|
||||||
|
"version": 3
|
||||||
|
}
|
||||||
|
|
@ -81,7 +81,7 @@ def header():
|
||||||
return doc
|
return doc
|
||||||
|
|
||||||
|
|
||||||
def asciidoc(content=False, t='title', title='', typename=''):
|
def asciidoc(content=False, t='title', title='', typename='', uuid=None):
|
||||||
adoc = []
|
adoc = []
|
||||||
adoc += "\n"
|
adoc += "\n"
|
||||||
output = ""
|
output = ""
|
||||||
|
|
@ -114,6 +114,7 @@ def asciidoc(content=False, t='title', title='', typename=''):
|
||||||
pass # ignore lookup errors
|
pass # ignore lookup errors
|
||||||
if output:
|
if output:
|
||||||
output = '{} has relationships with:\n{}\n'.format(title, output)
|
output = '{} has relationships with:\n{}\n'.format(title, output)
|
||||||
|
output = '\nlink:https://www.misp-project.org/graphs/{}.png[View relationships graph]\n\n{}\n'.format(uuid, output)
|
||||||
adoc += output
|
adoc += output
|
||||||
return adoc
|
return adoc
|
||||||
|
|
||||||
|
|
@ -139,7 +140,7 @@ for cluster in clusters:
|
||||||
if 'meta' in v:
|
if 'meta' in v:
|
||||||
adoc += asciidoc(content=v['meta'], t='meta-synonyms', title=v['value'])
|
adoc += asciidoc(content=v['meta'], t='meta-synonyms', title=v['value'])
|
||||||
if 'related' in v:
|
if 'related' in v:
|
||||||
adoc += asciidoc(content=v['related'], t='related', title=v['value'])
|
adoc += asciidoc(content=v['related'], t='related', title=v['value'], uuid=v['uuid'])
|
||||||
if 'meta' in v:
|
if 'meta' in v:
|
||||||
adoc += asciidoc(content=v['meta'], t='meta-refs', title=v['value'])
|
adoc += asciidoc(content=v['meta'], t='meta-refs', title=v['value'])
|
||||||
print(''.join(adoc))
|
print(''.join(adoc))
|
||||||
|
|
|
||||||
37
tools/generate-index.py
Executable file
37
tools/generate-index.py
Executable file
|
|
@ -0,0 +1,37 @@
|
||||||
|
#!/usr/bin/env python3
|
||||||
|
import json
|
||||||
|
import os
|
||||||
|
import argparse
|
||||||
|
|
||||||
|
|
||||||
|
parser = argparse.ArgumentParser(description='Generate a markdown index with all the galaxy available')
|
||||||
|
parser.add_argument("-v", "--verbose", action='store_true', help='Verbose output')
|
||||||
|
args = parser.parse_args()
|
||||||
|
|
||||||
|
|
||||||
|
def gen_galaxy_tag(galaxy_name, cluster_name):
|
||||||
|
# return 'misp-galaxy:{}="{}"'.format(galaxy_name, cluster_name)
|
||||||
|
return '{}={}'.format(galaxy_name, cluster_name)
|
||||||
|
|
||||||
|
galaxies_fnames = []
|
||||||
|
files_to_ignore = []
|
||||||
|
pathClusters = '../clusters'
|
||||||
|
|
||||||
|
for f in os.listdir(pathClusters):
|
||||||
|
if '.json' in f and f not in files_to_ignore:
|
||||||
|
galaxies_fnames.append(f)
|
||||||
|
|
||||||
|
galaxies_fnames.sort()
|
||||||
|
output = ""
|
||||||
|
|
||||||
|
for f in galaxies_fnames:
|
||||||
|
with open(os.path.join(pathClusters, f)) as fr:
|
||||||
|
cluster = json.load(fr)
|
||||||
|
output = f'{output}\n## {cluster["name"]}\n\n'
|
||||||
|
link = cluster["name"].replace(" ", "_").lower()
|
||||||
|
total = len(cluster["values"])
|
||||||
|
output = f'{output}[{cluster["name"]}](https://www.misp-project.org/galaxy.html#_{link}) - {cluster["description"]}\n'
|
||||||
|
output = f'{output}\nCategory: *{cluster["category"]}* - source: *{cluster["source"]}* - total: *{total}* elements\n'
|
||||||
|
output = f'{output}\n[[HTML](https://www.misp-project.org/galaxy.html#_{link})] - [[JSON](https://github.com/MISP/misp-galaxy/blob/main/clusters/{f})]\n'
|
||||||
|
|
||||||
|
print(output)
|
||||||
Loading…
Reference in a new issue